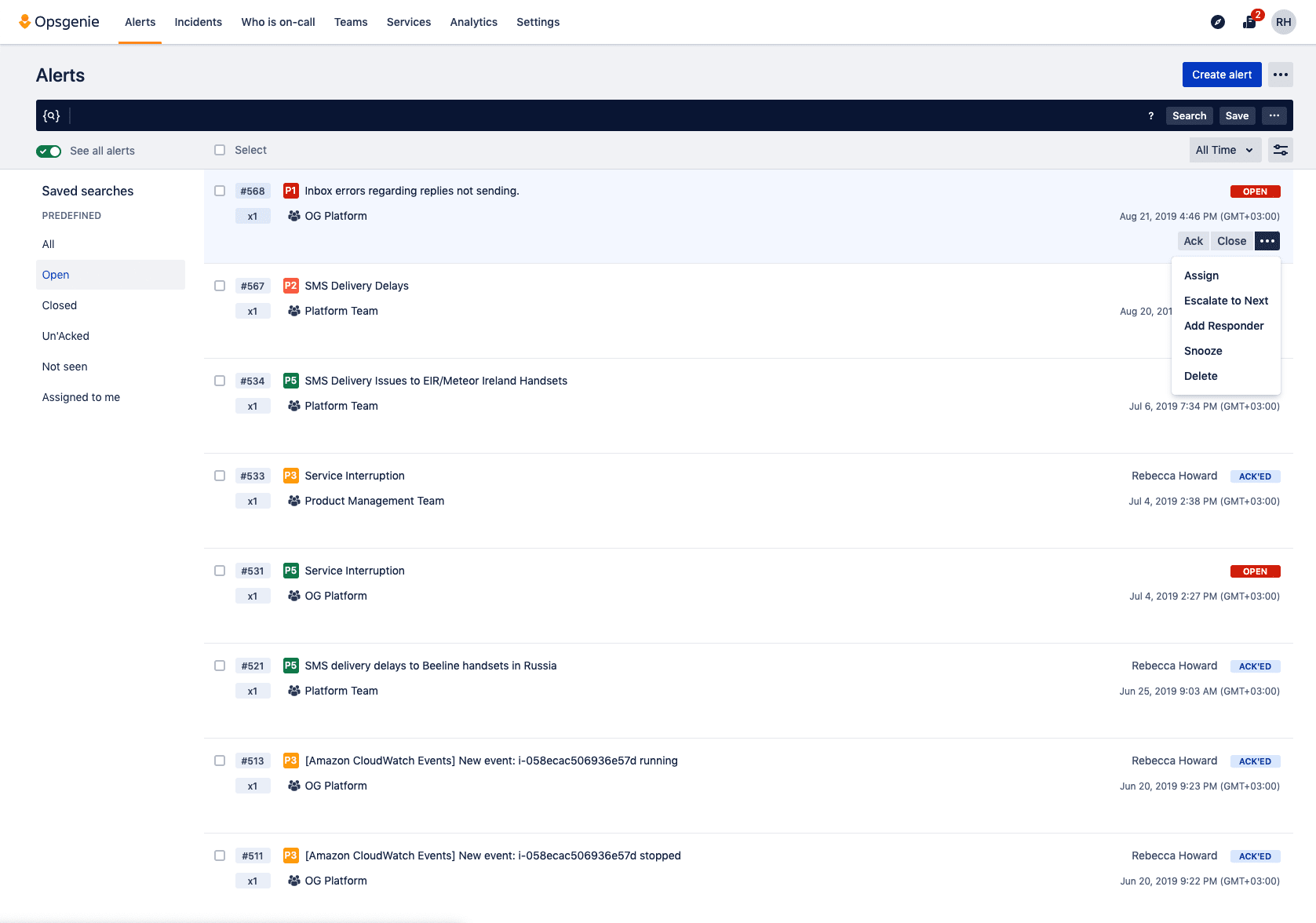
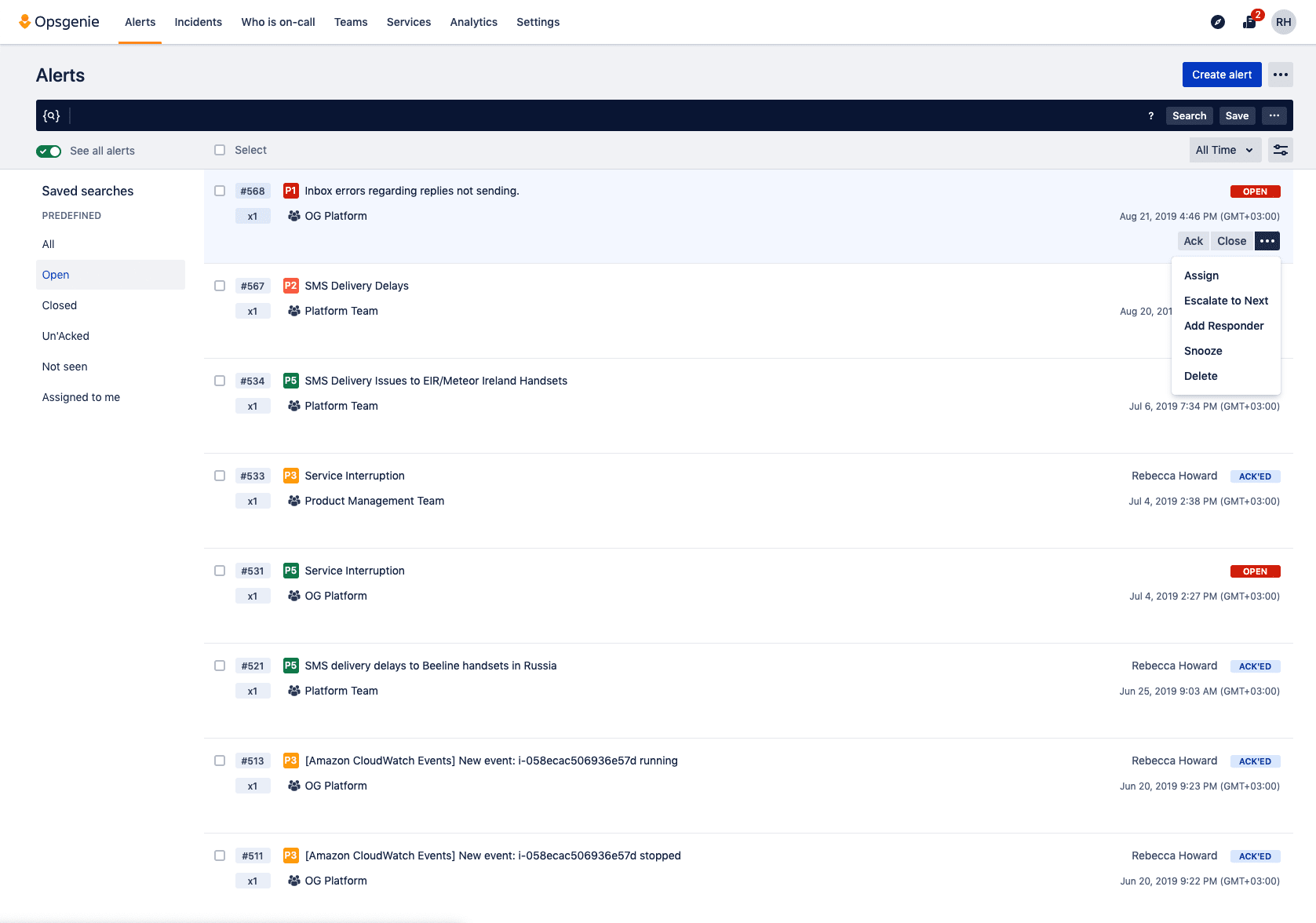
On-call and alert management to keep services always on
Centralize alerts and notify the right people at the right time
Never miss a critical alert
Flexibility to fit any workflow
Dynamic reporting and analytics
Incident Investigation
There are three ways to get started with Opsgenie

Opsgenie is available as a standalone offering that integrates into any IT or dev stack.
Opsgenie functionality is included across various cloud plans of Jira Service Management to deliver end-to-end incident management.

Opsgenie is included with Atlassian Open DevOps to help teams streamline incident management and response.

Learn why Looker trusts Opsgenie to help deliver always-on services to thousands of users daily.





Learn more about incident management
.png?cdnVersion=1567)
Incident Management Guide
The Five Stages of Incident Management
Introduction to Opsgenie
Start for free, scale as you grow
Essentials
Basic Alerting and On-Call Management, Optimized for Simplicity
Standard
Advanced Alerting and On-Call Management, Built for Flexibility
Enterprise
Service-Aware Incident Management